|
In the
news
"For
Some, Spying Controversy Recalls a Past Drama"
By Scott Shane
New York Times
February 6, 2006
"Spirited
wiretap debate of '76"
By Tom Brune
Newsday
February 5, 2006
"Papers:
Ford White House Weighed Wiretaps"
By
Margaret Ebrahim
Associated Press (via WashingtonPost.com)
February 4, 2006
Related
posting
The
National Security Agency Declassified
|
Washington,
D.C., February 4, 2006 - Despite
objections from then-Secretary of Defense Donald Rumsfeld and then-CIA
director George H. W. Bush, President Gerald Ford came down on the
side of a proposed federal law to govern wiretapping in 1976 instead
of relying on the "inherent" authority of the President
because the "pros" outweighed the "cons," according
to internal White House documents obtained through the Freedom of
Information Act and posted on the Web today by the National Security
Archive at George Washington University.
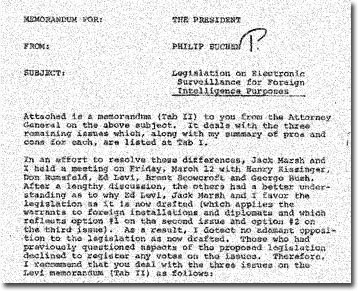 |
| After
much debate, the Ford administration in 1976 decided
to support legislation requiring a warrant for the government
to conduct electronic surveillance within the U.S. for
foreign intelligence purposes, according to this
memorandum prepared for President Ford by his counsel,
Philip Buchen.
|
|
White House counsel Philip Buchen described
a Situation Room meeting on March 12, 1976 with Rumsfeld,
Secretary of State Henry Kissinger, Bush, national security adviser
Brent Scowcroft, and attorney general Edward Levi (notably absent
was White House chief of staff Richard Cheney) in which Buchen's
and Levi's outline
of the advantages of a wiretapping law reduced the
"adamant opposition" to neutrality, allowing Levi to testify
before Congress in favor of a wiretapping statute on March 29, 1976.
Buchen's talking points said the proposed law (ultimately enacted
as the Foreign Intelligence Surveillance Act of 1978, or FISA) "avoids
likelihood that … courts will eventually decide a warrant
is required," "eliminates question of validity of evidence
obtained," "protects cooperating communications carriers,"
and would not "materially inhibit surveillance of these kinds
of targets."
On the "cons" side of his talking points, Buchen described
exactly the arguments against such a law that the Bush administration
has now adopted as the basis for its warrantless wiretapping: "requires
resort to the judiciary for exercise of an inherent Executive power"
and "could result in troublesome delays or even a denial of
authority in particular cases."
"Yogi Berra was right, the current wiretapping debate is déjà
vu all over again, except that President Bush has come down on the
con side against the law," remarked Thomas Blanton, director
of the National Security Archive.
 |
|
Chief of Staff Donald Rumsfeld, President Gerald Ford
and Deputy Chief of Staff Richard Cheney at the White
House, April 28, 1975 (Photo: Gerald R. Ford Presidential
Library)
|
|
Today's posting also includes the TOP SECRET Justice Department
reports in June 1976
and March 1977
on the potential criminal liability of the National Security Agency
and the Central Intelligence Agency for operations such as SHAMROCK
(interception of all international cable traffic from 1945 to 1975)
and MINARET (use of watchlists of U.S. dissidents and potential
civil disturbers to provide intercept information to law enforcement
agencies from 1969 to 1973). Justice released these reports to author
James Bamford under the Freedom of Information Act in the late 1970s,
but in 1981, the NSA persuaded Justice to threaten Bamford with
prosecution for "possession of classified information,"
a threat that helped Bamford's book The Puzzle Palace become
a best-seller.
The Justice Department in the reports ultimately recommended against
prosecution, concluding that "If the intelligence agencies
possessed too much discretionary authority with too little accountability,
that would seem to be a 35-year failing of Presidents and the Congress
rather than the agencies" (p. 171, 30 June 1976).
"Federal employees who are carrying out President Bush's warrantless
wiretapping will be especially interested in the Justice Department's
1976 assessment of whether such wiretapping makes them criminally
liable," commented Blanton. "One of the main reasons the
Ford administration supported having a law that governed wiretapping
was that such a law would protect government officials and the telecom
companies as long as they followed the law."
The Archive's posting, compiled by senior fellow Dr. Jeffrey Richelson
(author of the forthcoming book, Spying on the Bomb), includes
key historic documents brought to light by the Church Committee
investigations of intelligence abuses, and a series of National
Security Agency documents from the 1990s released under the Freedom
of Information Act that describe the limits imposed by FISA and
the Fourth Amendment on surveilling U.S. persons.
The posting also includes two important studies by the now-defunct
Office of Technology Assessment in 1985 and 1995 on the challenges
of electronic surveillance and civil liberties in a digital age,
as well as a wide range of key documents from the current wiretapping
debate, as featured on the www.cnss.org/fisa
web site (complete legislative history of the FISA), the www.fas.org
web site (the Project on Government Secrecy has published the relevant
Congressional Research Service studies, among other important documents),
and www.epic.org
which published the FBI's 2002 guide, "What
do I have to do to get a FISA?"
Electronic
Surveillance
From the Cold War to Al-Qaeda
National
Security Archive Electronic Briefing Book No. 178
Edited
by Jeffrey Richelson and Thomas Blanton
On December 16, 2005, The New York Times published a front-page
story revealing that months after Al-Qaeda's September 11, 2001
attacks on the United States, President George W. Bush formally
authorized the National Security Agency to monitor telephone conversations
and e-mails of Americans and other individuals, originating in the
United States, without the court-approved warrants usually required
for domestic surveillance. The monitoring program was reported to
consist of targeting the telephone and e-mail communications of
hundreds and perhaps thousands of people inside the United States
- with about 500 being monitored at any one time. Purely domestic
communications, according to the story, were still monitored only
after a warrant was obtained from the Foreign Intelligence Surveillance
Court (FISC). (Note 1)
Further reporting, since the initial revelation by the Times,
has added to information and claims about the program. It has become
known that NSA began the warrantless eavesdropping effort prior
to receiving formal approval from President Bush; that the operation
involved NSA obtaining the cooperation of American telecommunication
companies, which allowed the agency to tap "directly into some
of the American telecommunication system's main arteries";
that the information gathered was turned over to other agencies,
including the Defense Intelligence Agency, which compared the information
with data from other sources; and some purely domestic communications
(which both originated and terminated in the United States) were
accidentally intercepted. (Note 2)
The revelations about the eavesdropping program have produced numerous
editorials (for and against), discussion of why the administration
decided to by-pass the surveillance court, questions from the judges
on the Foreign Intelligence Surveillance Court, criticism and support
of the program from members of Congress on both sides of the aisle,
and defense of the program, in oral and written form, from the president,
vice-president, senior intelligence officials, and the Justice Department.
The legality of the program, the adequacy of administration briefings
to members of Congress, and the program's effectiveness have been
challenged and defended. Two inquiries are planned or in progress-a
Congressional inquiry as well as investigation by NSA's inspector
general-and two lawsuits have been filed demanding that the program
he halted immediately. (Note 3)
The controversy surrounding the program is not the first controversy
concerning whether U.S. signals intelligence and electronic surveillance
activities might compromise the Fourth Amendment rights of U.S.
persons. (Note 4) In the years immediately prior
to 9/11, press coverage of the NSA's ECHELON program-the placement
of computer software at selected satellite ground stations operated
by the NSA and key allies that allowed keyword sorting of some of
the international communications relayed through commercial communications
satellites and intercepted at those ground stations-resulted in
concern that the privacy of Americans (as well as foreign nationals)
would be sacrificed for the needs of U.S. foreign intelligence collection.
(Note 5)
In the mid-1970s, several decades before ECHELON became an issue,
as a result of a Senate investigation of intelligence community
activities, it had been revealed that NSA had been conducting two
programs of questionable propriety. One, SHAMROCK, originated in
the days just after the conclusion of the Second World War. It involved
U.S. communications companies giving NSA access to the cable traffic
passing through the companies' facilities. The second, MINARET,
created a watch list of U.S. persons-including military deserters
and those involved in civil disturbances and antiwar movements and
demonstrations-whose communications were to be monitored. Included
on the watch list were a number of anti-war activists, including
Joan Baez, Jane Fonda and Dr. Benjamin Spock. (Note
6)
The concern over NSA's domestic intelligence activities resulted
in the 1978 passage of the Foreign Intelligence Surveillance Act
(FISA). The Act established the three-judge Foreign Intelligence
Surveillance Court to review applications for monitoring the communications
(at the time, almost exclusively conventional telephone communications)
of U.S. persons suspected of involvement in espionage or terrorist
activities. It also created a review process in the event the U.S.
government was displeased with the court's decision.
The requirement to obtain court-orders for wiretaps of U.S. persons
did not prevent NSA from intercepting the communications of Americans
when the intercept was the result of targeting a non-U.S. person
at a communications node outside of the United States - an activity
whose legality survived a challenge before the Supreme Court. But
NSA operated under restrictions concerning how much information
about the American participating in the intercepted conversation
could be incorporated in intelligence reports or employed for law-enforcement
purposes. In many cases the name or other identifying information
would have to be removed and replaced by a term such as "U.S.
person." Such restrictions were first codified in the 1980
United States Signals Intelligence Directive "Limitations and
Procedures in Signals Intelligence Operations of the USSS"
(USSID 18), which was updated in 1993. (Note 7)
The collection of documents concerning U.S. electronic surveillance
activities presented here stretch from the later Cold War years
to today. Among the documents included are memoirs of the SHAMROCK
investigation, pre-9/11 NSA memos on electronic surveillance, several
expressions of Congressional concern concerning the current warrantless
eavesdropping program, a variety of administration defenses of the
program, and several Congressional Research Service analyses of
the legality of the program and the adequacy of administration briefings
to Congress.
Documents
Note: The following documents are in PDF format.
You will need to download and install the free Adobe
Acrobat Reader to view. Document
1: National Security Agency, Charter for Sensitive SIGINT
Operation MINARET, July 1, 1969. Classification Not Available
Source: Senate Select Committee to Study Governmental
Operations with Respect to Intelligence Activities, The National
Security Agency and Fourth Amendment Rights (Washington, D.C.:
U.S. Government Printing Office, 1976) via http://www.aarclibrary.org
This memo, from an assistant director of NSA, establishes the MINARET
program and notes that it specifically includes communications "concerning
individuals or organizations involved in civil disturbances, anti-war
movements/demonstrations and military deserters involved in anti-war
movements" and information on organizations or governments
that might influence them. It also notes that an important reason
for establishing the program is to restrict knowledge that such
information is being collected and processed by NSA.
Document
2: Vice Admiral Noel Gayler, Director, National Security Agency,
Memorandum for the Secretary of Defense, The Attorney General,
January 26, 1971. Classification Not Available
Source: Senate Select Committee to Study Governmental
Operations with Respect to Intelligence Activities, The National
Security Agency and Fourth Amendment Rights (Washington, D.C.:
U.S. Government Printing Office, 1976) via http://www.aarclibrary.org
The director of NSA prepared this memo following a meeting with
the Attorney General and Secretary of Defense, spelling out "the
agreed ground rules on NSA contributions to intelligence bearing
on domestic problems." Specific topics covered include the
character of the NSA activity, as well as the source of intercepted
communications, the operations scope, and procedures to be followed.
Document
3: Attorney General Elliot Richardson, Letter, to Lt. General
Lew Allen Jr., Director National Security Agency, October 1, 1973.
Classification Not Available
Source: Senate Select Committee to Study Governmental
Operations with Respect to Intelligence Activities, The National
Security Agency and Fourth Amendment Rights (Washington, D.C.:
U.S. Government Printing Office, 1976) via http://www.aarclibrary.org
In this letter the Attorney General informs the director of NSA
that he has recently discovered NSA had been disseminating intelligence
to the FBI and Secret Service obtained through NSA electronic surveillance
operations, conducted in response to requests from those agencies.
Richardson goes on to request that NSA refrain from providing further
intercept-derived domestic intelligence to other agencies until
he further considers the implication of a recent court decision.
Document
4: Lt. Gen. Lew Allen Jr., Director, National Security Agency,Letter,
to Honorable Elliot L. Richardson, October 4, 1973. Classification
Not Available
Source: Senate Select Committee to Study Governmental
Operations with Respect to Intelligence Activities, The National
Security Agency and Fourth Amendment Rights (Washington, D.C.:
U.S. Government Printing Office, 1976) via http://www.aarclibrary.org
In his response to the Attorney General's October 1 letter (Document
3), NSA director Allen tries to alleviate Richardson's concerns.
He notes that the messages passed on to organizations such as the
FBI and Secret Service are based on a watch list, and are "always
by-products of the foreign communications we intercept in the course
of our . . . foreign intelligence activities" -- but that he
has directed that, pending legal advice, no further information
be disseminated to the FBI and Secret Service.
Document
5: Gerald R. Ford, Memorandum for the Attorney General,
December 19, 1974. Top Secret
Source: Gerald R. Ford Library
In this memo, President Gerald Ford "reaffirms and renews"
the delegation of power to the Attorney General to approve, "without
prior judicial warrant," specific electronic surveillance within
the United States. The memo gives standards and procedures for the
exercise of that authority, including specification that the electronic
surveillance is necessary for one of four reasons, and that the
subject of the surveillance "is assisting a foreign power or
foreign-based political group, or plans unlawful activity directed
against a foreign power or foreign-based political group."
It does not impose any restrictions based on the nationality or
residence of the target of the proposed surveillance.
Document
6: Philip W. Buchen, Memorandum for: The President, Subject:
Warrantless Electronic Surveillance, August 13, 1975. Top Secret
Source: Gerald R. Ford Library
This memo to President Ford focuses on the concerns of different
departments with the provisions of President Ford's December 19
memorandum and the impact of a June 23, 1975 U.S. Court of Appeals
for the District of Colombia decision. The appeals court reversed
a lower court decision and declared unconstitutional warrantless
electronic surveillance of the Jewish Defense League (JDL), despite
the League's involvement in violent harassment of foreign government
officials, on the grounds that the JDL was a domestic organization
and was not the agent of, or acting in collaboration with, a foreign
power.
Document
7: Philip W. Buchen, Memorandum for: The President, Subject:
Warrantless Electronic Surveillance, January 12, 1976. Top
Secret/Sensitive
Document 7 [Tab C]: Edward
H. Levi, Memorandum for: The President, January 6, 1976.
Top Secret
Document 7 [Tab D draft]:
Memorandum for: The Attorney General, undated draft. Top
Secret
Document 7 [Tab D final]:
President Gerald R. Ford, Memorandum for: The Attorney General,
January 12, 1976. Top Secret
Source: Gerald R. Ford Library, Philip Buchen Files,
Box No. 26, "National Security Advisor Chronological File"
Tab
B to the January 12 memo remains classified and is the subject of
a declassification review request by the National Security Archive.
In a series of several memos between the Ford White House and the
Department of Justice, dated late 1974 to early 1976, the administration
debated the legality of warantless electronic surveillance in the
U.S. The January 12 memo contained several attachments, including
the December 19, 1974 memo (Document 5), in
which the president endorsed the power of the Attorney General,
by delegation, to conduct such warrantless surveillance.
A January 6, 1976 memo from the AG (at Tab C) referred to two existing
National Security Agency operations: (1) "the monitoring of
the Soviets' interception of American telephone calls," and
(2) "the direct interception of radio communications between
terminals abroad and brtween a terminal in the United States and
a terminal abroad." The memo states that DOJ had been "reviewing"
these operations and had developed strict minimization procedures
for the first operation which would "bring the operation clearly
within the reasonableness requirement of the Fourth Amendment"
by limiting retention and dissemination of information collected.
Despite the December 19, 1974 delegation of authority to the AG,
Levi nonetheless sought the president's "confirmation"
of his interpretation of that memo before authorizing the specified
surveillance operations. Questions about the second surveillance
program remained unresolved.
Finally, Buchen attached at Tab D a response memo to the Attorney
General, which he recommended the President signed. The memo, "drafted
by the Attorney General and approved by the Secretary of Defense"
as well as by National Security Adviser Brent Scowcroft, states
that the referenced NSA surveillance operation was properly subject
to the December 19 delegation and could therefore be approved by
the AG with "such additional safeguards concerning minimization
and subsequent use as the special nature of those activities may
in [his] opinion require." A final version of the memo, dated
January 12, 1976, includes revised language directing the AG to
communicate to the president any decision to withhold or terminate
his authorization for any foreign intelligence surveillance operations;
this version bears President Ford's signature.
Document
8: Philip W. Buchen, Memorandum for: The President, Subject:
Legislation on Electronic Surveillance for Foreign Intelligence
Purposes, March 15, 1976. Top Secret
Document 8 [Tab 1]: Philip
W. Buchen, Talking Points, Meeting: March 12, 1976, at 10:30
a.m. in White House Situation Room, Subject: Legislation on Electronic
Surveillance for Foreign Intelligence Purposes, March 12, 1976
Source: Gerald R. Ford Library, Presdiential Handwriting
File, Box No. 31, "National Security Intelligence"
Tab
II to the March 15 memo remains classified and is the subject of
a pending declassification review request by the National Security
Archive.
After much debate, the Ford administration in 1976 decided to support
legislation requiring a warrant for the government to conduct electronic
surveillance within the U.S. for foreign intelligence purposes,
according to a memorandum prepared for President Ford by his counsel,
Philip Buchen. "In an effort to resolve ... differences"
among the key players in the administration on the matter, Buchen
and Counselor to the President Jack Marsh convened a meeting on
March 12, 1976 in the White House situation room; in attendance
were Secretary of State Henry Kissinger, Secretary of Defense Donald
Rumsfeld, National Security Advisor Brent Scowcroft, CIA Director
George Bush, and Attorney General Ed Levi. White House Chief of
Staff Dick Cheney was notably absent from this meeting. After a
"lengthy discussion," Buchen was satisfied that "the
others had a better understanding as to why" he, Marsh, and
Levi favored the legislation as drafted, and he "detect[ed]
no adamant opposition" remaining from "those who had previously
questioned aspects of the proposed legislation." Congress ultimately
followed the administration's recommendation when it enacted FISA
in 1978.
In accompanying talking points prepared for the meeting, Buchen
outlined the pros and cons of the statutory approach. In particular,
he favored the requirement of a warrant for surveillance because
such an approach "[a]voids likelihood that in absence of legislation,
courts will eventually decide a warrant is required in such cases,"
"[e]liminates question of validity of evidence obtained,"
"[p]rotects cooperation communications carriers and landlords
and protects against charges of criminal trespasses," and "[a]voids
having legislation which is designed solely to permit [redacted]
when such activities are relatively a minor portion of the electronic
surveillance program and key members of the Senate Judiciary Committee
want the legislation to include [redacted] surveillance"; moreover,
"[t]he stated tests for obtaining a warrant are not of a kind
which will materially inhibit surveillance of these kinds of targets."
Anticipating counter-arguments, the document presents potential
challenges to the legislation as drafted, including that it "[u]nnecessarily
requires resort to the judiciary for exercise of an inherent Executive
power, especially in cases where only communications of [redacted]
are involved"; "[m]akes warrants mandatory even in the
area of communications [redacted] that are not of significant concern
to the Congress, when warrants in cases [redacted] might better
be made optional in the discretion of the Executive"; and "[c]ould
result in troublesome delays or even a denial of authority in particular
cases." He also weighs the specifics of the test on which decisions
to grant warrants would be based.
On March 29-30, 1976, Attorney General Levi testified before the
Senate Judiciary Committee <http://www.cnss.org/fisa032976.pdf>
in support of the Foreign Intelligence Surveillance Act.
Document
9a: Department of Justice, Report on the Inquiry into CIA-Related
Electronic Surveillance Activities, June 30, 1976. Top Secret
Document
9b: Department of Justice, George W. Calhoun, Chief, Special
Litigation, Memorandum for: Robert L. Keuch, Deputy Assistant Attorney
General, Subject: Prosecutive Summary, March 4, 1977. Top Secret.
Source:
James Bamford, Freedom of Information Act Request. See Bamford,
"Big brother is listening: Why this article will be closely
read at the National Security Agency," Washington Post
Magazine, December 4, 1983, p. 34.
These two documents report on the findings of a Department of Justice
inquiry conducted to determine if criminal prosecutions of government
personnel were warranted based on their conduct of electronic surveillance.
The report addressed the findings of the Rockefeller Commission
(on CIA Activities), and examined a variety of CIA and NSA eavesdropping
operations, purported sources of authority for the operations, possible
violations of law, and possible defenses. The Justice Department
in the reports ultimately recommended against prosecution, concluding
that "If the intelligence agencies possessed too much discretionary
authority with too little accountability, that would seem to be
a 35-year failing of Presidents and the Congress rather than the
agencies" (p. 171, 30 June 1976). Justice released these reports
to author James Bamford under the Freedom of Information Act at
the end of the Carter administration, but in 1981, the NSA persuaded
Justice to threaten Bamford with prosecution for "possession
of classified information" if he did not return the documents,
a threat that helped Bamford's book The Puzzle Palace become
a best-seller.
Document
10:
U.S. Congress, Foreign Intelligence Surveillance Act, 1978.
Unclassified
Source:
Center for National Security Studies, Foreign Intelligence Surveillance
Act, Legislative History, at http://www.cnss.org/fisa.htm.
In response to revelations concerning the MINARET and SHAMROCK
programs, Congress passed this act to codify the process of authorizing
electronic surveillance for foreign intelligence purposes. It created
the Foreign Intelligence Surveillance Court and defined its responsibilities,
specified the process for obtaining warrants, and established a
court of review.
Document
11: Jimmy Carter, Executive Order 12139, Foreign Intelligence
Electronic Surveillance, May 23, 1979. Unclassified
Source:
Federal Register, 44, 103, May 25, 1979
In this executive order, President Carter authorizes the Attorney
General to approve warrantless electronic surveillance in order
to obtain foreign intelligence if the Attorney General makes the
certifications required according to the Foreign Intelligence Surveillance
Act-that the means of communications being used are exclusively
between or among foreign powers or the objective is collect technical
intelligence from property or premises under the "open and
exclusive" control of a foreign power, and that there is no
substantial likelihood that the surveillance will acquire the contents
of any communication involving a United States person.
Document
12: Office of Technology Assessment, Electronic Surveillance
and Civil Liberties, 1985. Unclassified
Source:
Government Printing Office
This report, by the now-defunct Congressional Office of Technology
Assessment (OTA), examines how changes in technology-including the
introduction of cordless and cellular telephones -- would or could
impact the opportunities for and vulnerabilities to electronic surveillance,
and the consequences for civil liberties.
Document
13a: National Security Agency, Foreign Intelligence Surveillance
Act, no date. For Official Use Only
Document 13b: National
Security Agency, The Five Electronic Surveillance Questions,
no date. Top Secret
Source: Freedom of Information Act Request
These undated documents (from sometime in the 1990s), provide a
brief summary of key questions involved in implementation of the
FISA. Document 11a distinguishes four categories of electronic surveillance
and defines targets, U.S. persons, and contents. Document 11b poses
questions and provides answers concerning the nature and location
of the target, as well as the communications to be intercepted.
Document
14: National Security Agency, Summary of the Main Provisions
of USSID 18, September 3, 1991. Secret
Source:
Freedom of Information Act Request
This summary provides a list of do and don't concerning the collection,
processing, retention, and dissemination of intercepted communications
involving a U.S. person.
Document
15: Office of Technology Assessment, Electronic Surveillance
in a Digital Age, July 1995. Unclassified
Source:
Government Printing Office
This study, written a decade after the OTA study on electronic
surveillance and civil liberties (Document 7)
focuses on electronic surveillance for law-enforcement, rather than
foreign intelligence, purposes. Its relevance lies in its treatment
of how the changing technology of communications in the digital
age (circa 1995)-including fiber optics and the use of computers
for directing and processing calls-influences law enforcement agencies'
ability to conduct electronic surveillance.
Document
16: National Security Agency, Standard Minimization Procedures
for NSA Surveillance, no date (but after July 1, 1997). Secret
Source:
Freedom of Information Act Request
These guidelines, approved by Attorney General Janet Reno on July
1, 1997, pertain to the acquisition, retention, use, and dissemination
of non-publicly available information concerning non-consenting
U.S. persons collected in the course of electronic surveillance
approved by the Foreign Intelligence Surveillance Court or authorized
by the Attorney General under the provisions of the FISA.
Document
17: National Security Agency, Collection, Processing, Retention,
and Dissemination of "Domestic" Communications under the
Foreign Intelligence Surveillance Act - INFORMATION MEMORANDUM,
February 25, 1998. Secret
Source:
Freedom of Information Act Request
Domestic communications are defined in this memo as any communication
with both parties in the United States except when both parties
are foreign powers and/or officers or employees of foreign powers
(also referred to as "agents of a foreign power"). As
the memo's title indicates, it focuses on various aspects of the
handling of domestic communications required by the Foreign Intelligence
Surveillance Act.
Document
18: L. Britt Snider, "Recollections from the Church Committee's
Investigation of NSA," Studies in Intelligence, Winter
1999/2000, pp. 43-51
Source:
http://www.cia.gov/csi/studies/winter99-00/art4.html
This article represents the recollections of staff member of the
Select Committee to Study Governmental Operations with Respect to
Intelligence Activities (better known as the Church Committee),
which investigated the SHAMROCK program as part of its broader 1975
inquiry into the activities of the U.S. Intelligence Community.
Document
19: National Security Agency, Legal Standards for the Intelligence
Community in Conducting Electronic Surveillance, February 2000.
Unclassified
Source:
http://www.fas.org/irp/nsa/standards.html
The Fiscal Year 2000 Intelligence Authorization Act required that
the National Security Agency transmit a report summarizing the agency's
understanding of the legal standards that authorized and constrained
the electronic surveillance activities of the Intelligence Community.
Topics covered include legal standards for (1) intercepts when the
result may involve the acquisition of information from communications
to or from a U.S. person; (2) for intentional targeting of communications
to or from U.S. persons; (3) for receipt from non-U.S. sources of
information pertaining to communication to or from United States
persons; and (4) for the dissemination of information acquired through
the interception of the communications to or from United States
persons.
Document
20: Lt. Gen. Michael V. Hayden, NSA/CSS Operates Under the
Rule of Law, April 12, 2000. Unclassified
Source:
http://www.nsa.gov/releases/HPSCI_04122000/
This PowerPoint presentation, before the House Permanent Select
Committee on Intelligence, was a response by NSA Director Hayden
to the reports in the American and European press over the ECHELON
program. Among the topics covered in the presentation are press
claims, protections for U.S. persons, the FISA process, the aftermath
of unintentional acquisition of information on U.S. persons, the
restrictions on NSA activity imposed by the Constitution, federal
laws, executive orders, regulations, and the oversight of compliance.
Document
21: Rules of the Foreign Intelligence Surveillance Court,
November 29, 2000. Unclassified
Source: http://www.fas.org
This document specifies, inter alia, the duties of the
presiding judge, the powers of individual judges, rules concerning
submission of applications, procedure on denial of applications,
when the court meets, and its rules of decision.
Document
22a: Letter, Representative Nancy Pelosi to Lt. Gen. Michael
V. Hayden, Director, National Security Agency, October 11, 2001.
Top Secret
Document 22b: Letter,
Lt. Gen. Michael V. Hayden, Director, National Security Agency to
Representative Nancy Pelosi, October 18, 2001. Secret
Source:
http://www.house.gov/pelosi/press/releases/Jan06/declassified.html
These two documents are an exchange of letters from October 2001,
written by then-ranking member on the House Permanent Select Committee
on Intelligence (HPSCI) Nancy Pelosi to National Security Agency
Director Michael V. Hayden. In her letter, Pelosi expresses concerns
regarding the electronic surveillance activities about which Hayden
had testified in his October 1 appearance before the HPSCI. In his
response, Hayden notes that his briefing was an attempt to "emphasize
that I used my authorities to adjust NSA's collection and reporting."
Document
23: Department of Justice, In Re [deleted] on Appeal from
the United States Foreign Intelligence Surveillance Court, Brief
for the United States, No. 02-001, August 21, 2002. Classification
Not Available
Source:
http://www.fas.org
In August 2002, the Department of Justice appealed the Foreign
Intelligence Surveillance Court modification of an application for
a FISA warrant, arguing that the act did not restrict the government's
intention to use foreign intelligence information in criminal prosecutions.
It further argued that even had the law imposed such restrictions
they were revoked by the provisions of the PATRIOT Act.
Document
24: Federal Bureau of Investigation, What do I have to do
to get a FISA?, September 12, 2002. Classification Not Available
Source:
http://www.epic.org
This memo provides a primer for FBI personnel on applying for
a FISA warrant. It discusses the FISA Court, probable cause, the
theory of the case, the importance of the target of the proposed
surveillance being an agent of a foreign power, and certification.
Document
25: United States Foreign Intelligence Surveillance Court of
Review, In re: Sealed Case No. 02-001, Consolidated with 02-002,
November 18, 2002. Classification Not Available
Source:
http://www.cnss.org/fisa.htm
This document conveys the decision of the FISA review court, which
granted the Department of Justice's appeal (Document
23). In its conclusion the review court refers to "the
President's inherent constitutional authority to conduct warrantless
foreign intelligence surveillance."
Document
26: Letter, John Ashcroft, Attorney General to L. Ralph Mecham,
Director, Administrative Office of the United States Courts, April
29, 2003. Unclassified
Source:
http://www.epic.org
This letter from Attorney General Ashcroft constitutes the Department
of Justice's annual report on FISA applications. Ashcroft notes
that with the FISA review court's reversal of the FISC's two modifications
of FISA warrant applications (Document 12)
all 1228 warrant applications for 2002 were granted.
Document
27: Letter, Senator Jay D. Rockefeller to Vice President Richard
Cheney, July 17, 2003. Unclassified
Source:
http://www.epic.org
Senator Rockefeller's reservations about NSA's warrantless eavesdropping
program were expressed in this letter to Vice President Cheney,
without mention of any of the specifics. It was handwritten because
none of the Senator's aides were cleared to receive information
about the program.
Document
28: Elizabeth B. Bazan, Congressional Research Service, Intelligence
Reform and Terrorism Prevention Act of 2004: "Lone Wolf"
Amendment to the Foreign Intelligence Surveillance Act, December
29, 2004. Unclassified
Source:
http://www.fas.org
The Intelligence Reform and Terrorism Prevention Act of 2004 amended
the Foreign Intelligence Surveillance Act's definition of an "agent
of a foreign power" to include a non-U.S. person who engages
in international terrorism or activities in preparation for international
terrorism. This study analyzes whether and how the modified definition
impacts the procedures for seeking a FISA warrant, contents of FISA
applications, and the basis for court decisions granting a warrant.
Document
29: Elizabeth B. Bazan, Congressional Research Service, Foreign
Intelligence Surveillance Act: Selected Legislation from the 108th
Congress, January 11, 2005. Unclassified
Source:
http://www.fas.org
In the aftermath of the September 11 attacks, Congress considered
or passed a number of bills, the most prominent being the PATRIOT
Act, which affected or proposed changes to FISA provisions. This
analysis examines two categories of bills-intelligence reform or
reorganization proposals with FISA provisions and other FISA-related
bills-and the impact of their passage on the Act.
Document
30: Elizabeth B. Bazan, Congressional Research Service, The
Foreign Intelligence Surveillance Act: An Overview of the Statutory
Framework and Recent Judicial Decisions, April 21, 2005. Unclassified
Source:
http://www.fas.org
This study reviews both the statutory framework of the act as well
as examining the Foreign Intelligence Surveillance Court decision
that resulted in the government's August 2002 appeal, the appeal
(Document 23), and the decision of the FISC
Court of Review (Document 25).
Document
31: William E. Moschella, Assistant Attorney General, to Honorable
Arlen Specter w/att: Follow up Questions from Chairman Specter,
October 20, 2005, Unclassified
Source:
http://www.fas.org
In the attachment to his letter, the assistant Attorney General
provides answers to a number of questions posed by Senator Specter
in an April 2005 hearing before the Senate Judiciary Committee.
The questions concern the time required to obtain a surveillance
order under FISA, the factors related to the time required, and
whether the "Lone Wolf" provision has been employed (Document
17).
Document
32: The White House, President's Radio Address, December
17, 2005. Unclassified
Source:
http://www.whitehouse.gov
This address by President Bush occurred only a day after The
New York Times revealed that he had authorized NSA to conduct
warrantless electronic surveillance and represents the first of
a number of administration defenses of the program. After discussing
the status of the effort to renew the PATRIOT act, he turns to the
objectives, propriety, and review process connected with the eavesdropping
effort.
Document
33a: The White House, Press Conference of the President,
December 19, 2005. Unclassified
Source:
http://www.whitehouse.gov
Document 33b: Office of
the Director of National Intelligence, Press Briefing by Attorney
General Albert Gonzales and General Michael V. Hayden, Principal
Deputy Director of National Intelligence, December 19, 2005.
Unclassified
Source: http://www.dni.gov
Two days after his radio address, the president held a press conference
in which he discussed the warantless electronic surveillance program
in more detail. That same day, the Attorney General and the principal
deputy director of national intelligence held a press briefing at
the White House devoted solely to the eavesdropping activity. In
a brief statement before he and Hayden took questions, Gonzales
argued that the Congressional use-of-force resolution passed after
September 11 authorized the president to conduct surveillance and
further that "the President has the inherent authority under
the Constitution, as Commander-in-Chief, to engage in this kind
of activity."
Document
34: Letter, William E. Moschella to Senator Pat Roberts, Senator
John D. Rockefeller IV, Rep. Peter Hoekstra, and Rep. Jane Harman,
December 22, 2005. Unclassified
Source:
http://www.epic.org
This letter from the Assistant Attorney General to the chair and
vice chair of the Senate Select Committee on Intelligence and the
chair and ranking minority member of the House Permanent Select
Committee on Intelligence is the first written, unclassified, legal
opinion provided by the administration in defense of the post-9/11
warrantless electronic surveillance program. It refers to Article
II of the U.S. Constitution, the post-9/11 Congressional resolution
authorizing the use of force, and the November 18, 2002 decision
by the Foreign Intelligence Surveillance Court of Review (Document
16)
Document
35: The White House, Setting the Record Straight: Critics
Launch Attacks Against Program to Detect and Prevent Terrorist Attacks,
January 4, 2006. Unclassified
Source:
http://www.whitehouse.gov
In response to concerns and charges by four Democratic members
of Congress, this White House release contains sections devoted
to "setting the record straight" in four areas: on separate
NSA activities, on the terrorist ties of intercepted communications,
on the scope of the program, and on the use of the FISA court.
Document
36: Elizabeth B. Bazan and Jennifer K. Elsea, Congressional
Research Service, Presidential Authority to Gather Foreign Intelligence
Information, January 5, 2006. Unclassified
Source:
http://www.fas.org
This report challenges claims made by the president and other administration
officials concerning the legality of the program permitting warrantless
electronic surveillance that was approved by President Bush in October
2001. It disputes the assertion of presidential authority to bypass
the FISA court. It also challenges the assertion that the Congressional
resolution approved after the September 11 attacks represented an
explicit or implicit authorization of the warrantless eavesdropping
program.
Document
37: American Civil Liberties Union [and others] v. National
Security Agency/Central Security Service, Complaint for Declaratory
and Injunctive Relief, United States District Court, Eastern
District of Michigan, Southern Division, January 17, 2006. Unclassified
Source:
http://www.aclu.org
This complaint filed by the ACLU along with other organizations
and individuals "challenges the constitutionality of a secret
government program to intercept vast quantities of the international
telephone and Internet communications of innocent Americans without
court approval. The plaintiffs according to the complaint frequently
communicate by telephone and e-mail with people in the Middle East
and South Asia and "have a well-founded belief that their communications
are being intercepted."
Document
38: Alfred Cumming, Congressional Research Service, Statutory
Procedures Under Which Congress Is to Be Informed of U.S. Intelligence
Activities, Including Covert Actions, January 18, 2006. Unclassified
Source:
http://www.fas.org
This study claims that the Bush administration may have violated
a provision of the National Security Act by restricting its briefings
about warrantless domestic eavesdropping to Congressional leaders.
Rather, it is the analyst's conclusion that the law requires all
members of the House and Senate intelligence oversight committees
to be "fully and currently informed."
Document
39: U.S. Department of Justice, Legal Authorities Supporting
the Activities of the National Security Agency Described by the
President, January 19, 2006. Unclassified
Source:
http://www.usodj.gov
In response to continuing controversy the Justice Department released
this extensive 42-page brief. After discussing the background of
the eavesdropping program, NSA's activities, and the threat posed
by Al-Qaeda, the brief addresses a number of issues concerning the
legality of the program-whether the president has inherent constitutional
authority to order warrantless foreign intelligence surveillance,
whether the post-9/11 resolution passed by Congress (the Authorization
to Use Military Force (AUMF)) authorized the President to bypass
the FISA, and whether NSA's activities are consistent with the Foreign
Intelligence Surveillance Act and the Fourth Amendment.
Document
40: Office of the Director of National Intelligence, Remarks
by General Michael V. Hayden, What American Intelligence & Especially
the NSA Have Been Doing To Defend the Nation, January 23, 2006.
Unclassified
Source:
http://www.dni.gov
Hayden served as director of the National Security Agency from
March 1999 until his appointment as principal deputy director of
national intelligence in 2005. In his talk he sought to provide
reassurance that NSA was focused on foreign intelligence, that it
was not conducting "domestic spying" but was targeting
individuals believed to be associated with al-Qaeda, that it was
"not about" intercepting communications between individuals
in the United States, and that it did not involve processing masses
of data with keyword search. He also sought to explain why it was
necessary for the administration to bypass the FISA court.
Document
41: Attorney General Alberto R. Gonzales, Intercepting Al
Qaeda: A Lawful and Necessary Tool for Protecting America,
January 24, 2006. Unclassified
Source:
http://www.epic.org
In this speech at Georgetown University Law School, the Attorney
General cited the actions of past presidents in addition to citing
some of the previous arguments in support of the administration's
employment of NSA to conduct warantless electronic surveillance.
He mentions George Washington's use of secret intelligence obtained
from the interception of mail between the British and Americans,
President Woodrow Wilson's order to intercept of all cable communications
between the United States and Europe, and President Franklin D.
Roosevelt's authorization to intercept all communications into and
out of the United States.
Document
42: The White House, President Visits National Security
Agency, January 25, 2006. Unclassified
Source:
http://www.whitehouse.gov
This is a transcript of the president's remarks upon his visit
to NSA. The remarks include a brief explanation of why he considered
the NSA warrantless electronic surveillance program to be necessary,
a reference to the actions of previous presidents, and his promise
to continue to reauthorize the program as "long as our country
faces a continuing threat from al Qaeda and related groups."
Notes
1. James Risen and Eric Lichtblau, "Bush
Lets U.S. Spy on Callers Without Courts," New York Times,
December 16, 2005, pp. A1, A22.
2. Eric Lichtblau and James Risen, "Eavesdropping
Effort Began Soon After Sept. 11 Attacks," New York Times,
December 18, 2005, p. 31; Erich Lichtblau and Scott Shane, "Agency
FirstActed on Its Own To Broaden Spying, Files Show," New
York Times, January 4, 2006, pp. A1,A13; Eric Lichtblau and
James Risen, "Spy Agency Mined Vast Data Trove, Officials Report,"
New York Times, December 24, 2005, pp. A1, A12; Walter
Pincus, "NSA Gave Other U.S. Agencies Information From Surveillance,"
January 1, 2006, www.washingtonpost.com; James Risen and Eric Lichtblau,
"Spying Program Snared U.S. Calls," New York Times,
December 21, 2005, pp. A1, A23.
3. "This Call May Be Monitored," New
York Times, December 18, 2005, Sec. 4, p.11; "Thank You
for Wiretapping," Wall Street Journal, December 20,
2005, p. A14; Richard Lacayo, "Has Bush Gone Too Far?,"
January 1, 2006, www.time.com; Carol D. Leoning, "Surveillance
Court is Seeking Answers," January 5, 2006, www.washingtonpost.com;
Scott Shane, "Key Democrat Says Spying Violated Law,"
New York Times, January 5, 2006, p. A16; Scott Shane, "Republican
Senator Defends Briefings on Domestic Spying," New York
Times, January 6, 2006, p. A15; Lowell Bergman, Eric Lichtblau,
Scott Shane, and Don Van Natta Jr., "Spy Agency Data After
Sept. 11 Led F.B.I. to Dead Ends," New York Times,
January 17, 2006, pp. A1, A12; Dan Eggen, "Probe Set in NSA
Bugging," January 11, 2006, www.washingtonpost,com; Eric Lichtblau,
"Two Group Plan Lawsuits Over Federal Eavesdropping,"
New York Times, January 17, 2006, p. A12.
4. A U.S. person is defined as:
a citizen of the United States, an alien lawfully admitted for
permanent residence ..., an unincorporated association a substantial
number of members of which are citizens of the United States or
aliens lawfully admitted lawfully admitted for permanent residence,
or a corporation which is incorporated in the United States, but
does not include a corporation or an associated which is a foreign
power. Foreign Intelligence Surveillance Act, 50 U.S.C. §1801(i).
The Fourth Amendment provides:
The right of the people to be secure in their persons, houses,
papers, and effects, against unreasonable searches and seizures,
shall not be violated, and no Warrants shall issue, but upon probable
cause, supported by Oath or affirmation, and particularly describing
the place to be searched, and the persons or things to be seized.
U.S. Constitution amend. IV.
5. See Jeffrey T. Richelson, "Desperately
Seeking Signals," Bulletin of the Atomic Scientists,
March/April 2000, pp. 47-51.
6. James Bamford, The Puzzle Palace: A Report
on NSA, America's Most Secret Agency (Boston: Houghton-Mifflin,
1982), pp. 236-254; Bob Woodward, "Messages of Activists Intercepted,"
Washington Post, October 13, 1975, pp. A1, A14.
7. See National Security Archive Electronic Briefing
Book #24, Jeffrey Richelson, editor, The
National Security Agency Declassified, March 11, 2005, for USSID
18 and other USSID 18-related documents.
|

